Confidential means more than just encryption
Encrypted
Confide uses industry-standard end-to-end encryption to keep your messages safe and to ensure they can only be read by the intended recipients.
See MoreEphemeral
Messages disappear forever after they are read once, making them as private and secure as the spoken word.
See MoreScreenshot-Proof
Confide’s patented ScreenShield technology keeps your communication safe by preventing screenshots of your messages.
See MoreEncryption
Confide uses industry-standard end-to-end encryption to keep your messages safe.
Industry-Standard Cryptography
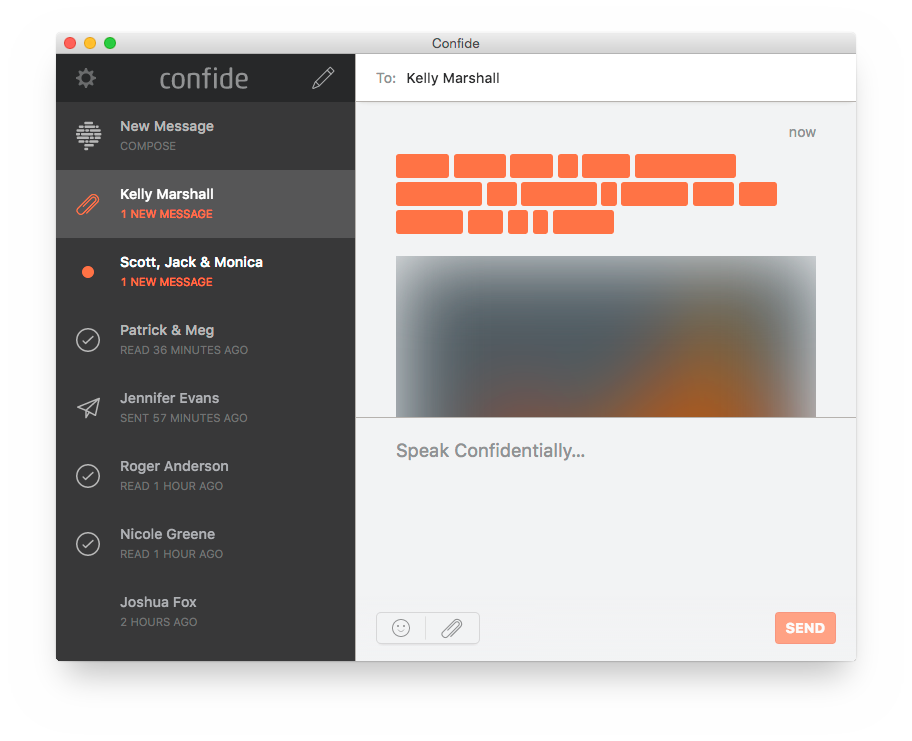
Confide utilizes industry-standard cryptography to keep your messages safe and secure. We combine this with a simple and intuitive user experience to provide superior security, with no configuration required.
End-to-End Encryption
All messages between Confide users are end-to-end encrypted. Encryption keys are generated locally on each device and the private key never leaves the device, ensuring that only the intended recipients can read your messages.
Transport Layer Security
All communication goes through Transport Layer Security (TLS), preventing any possible man-in-the-middle attack and providing yet another layer of security, privacy and data integrity.
Ephemeral
Encryption is an important component of confidentiality but it’s not the only one. After a message is decrypted it becomes vulnerable. It can be archived, printed and even forwarded. But Confide messages self-destruct. After they are read once, they are gone. We delete them from our servers and wipe them from the device. No forwarding, no printing, no saving … no nothing.
Screenshot-Proof
Screenshots have the potential of making the impermanent permanent. Confide prevents screenshots with our patented ScreenShield technology.
For extra privacy on iOS and Android, our patented reading experience ensures that only one line of the message is unveiled at a time and that the sender’s name is not simultaneously visible.
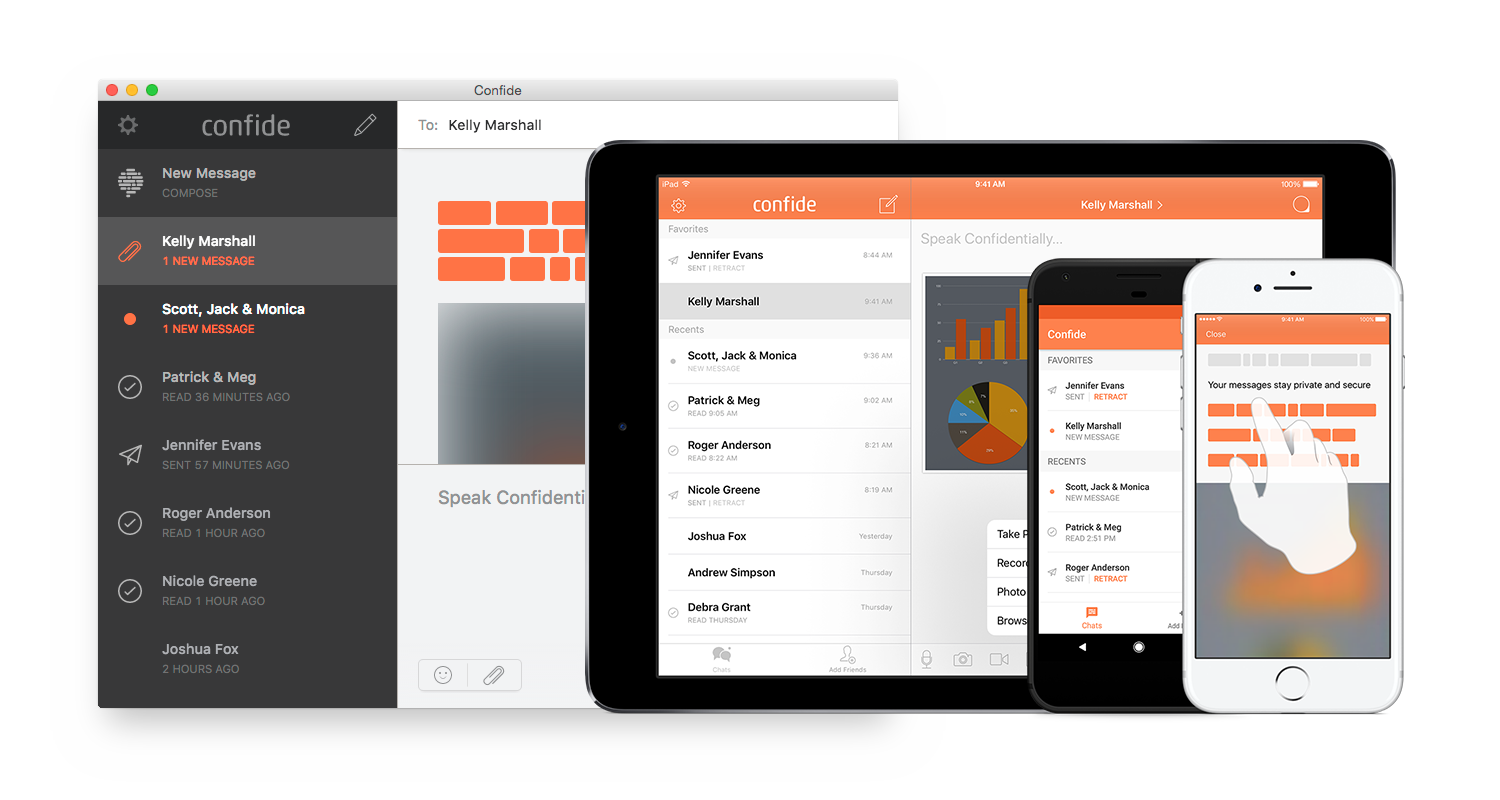
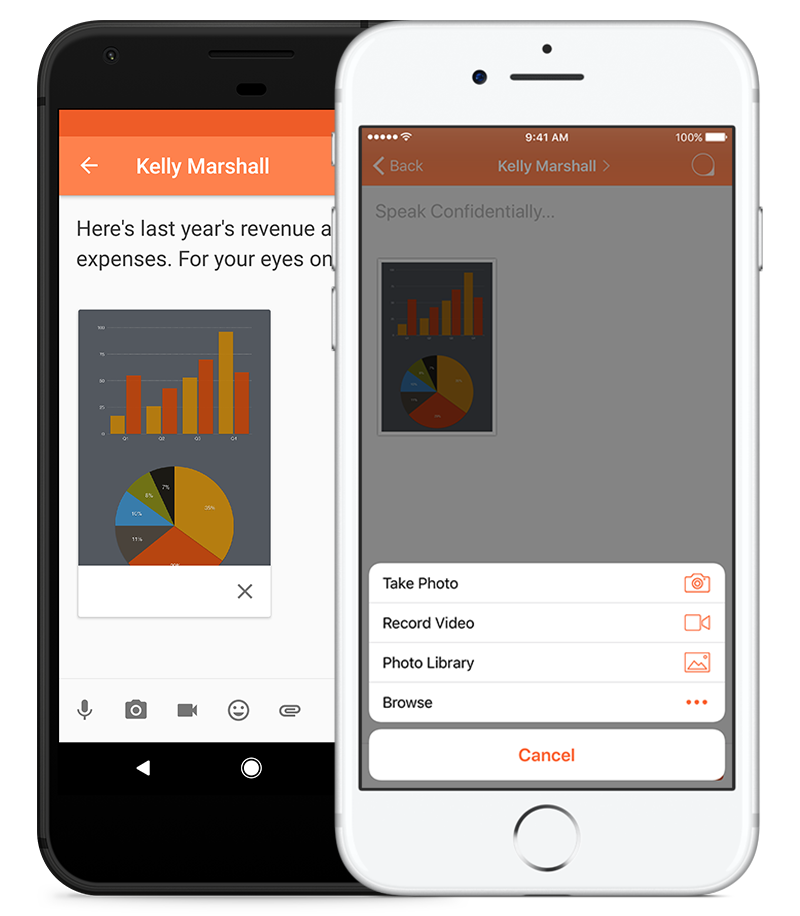
Photos, Videos, Documents, Voice & Group Messaging
Send text, photos, videos, documents and voice messages to individuals or groups. Like text, all photos, videos, documents and voice messages are encrypted, ephemeral and screenshot-proof. Communicate in whatever format you’d like, without leaving a copy behind.
Confide Plus Learn More
Subscribe to Confide Plus for more features and more control.
Unlimited Attachments
Send an unlimited number of Confide messages with an attachment — photo, video, document, voice message or sticker.
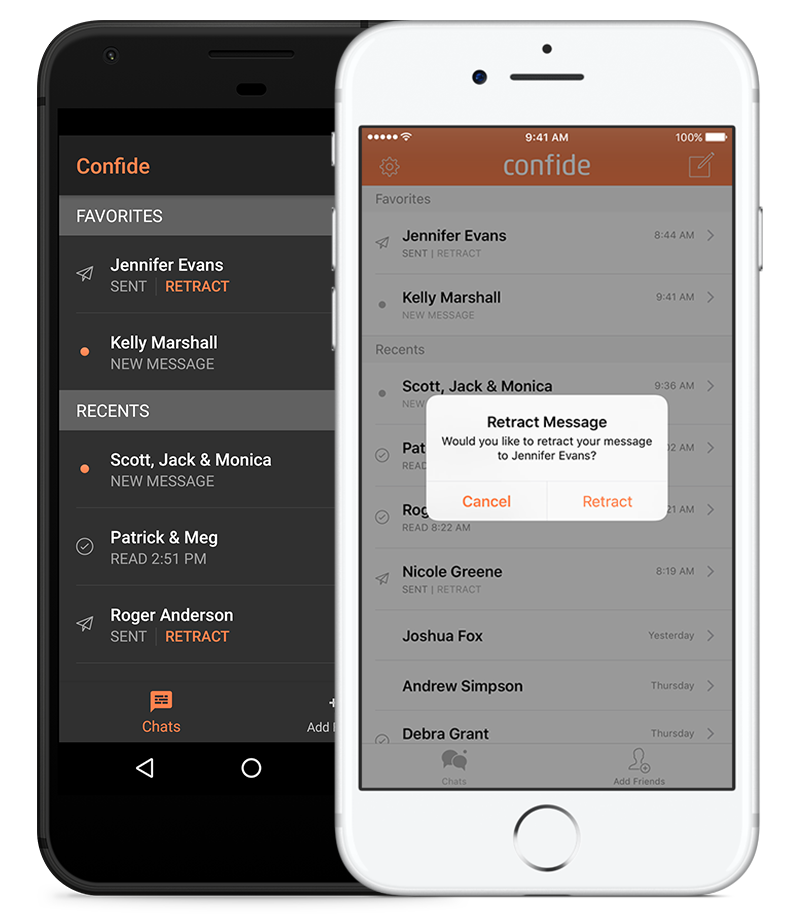
Message Retraction
We have all sent messages we wish we could take back. Message retraction allows you to retract (or “un-send”) unread messages.
Incognito Mode
Control your Confide presence. Incognito mode allows you to be hidden on Confide so you can’t be found by others.
Nicknames
Want to change the name of a contact? Create a nickname for them. Nicknames will only be seen by you and won’t be visible to your contacts.
Themes
Personalize your Confide app with custom themes. Whatever your mood, Confide has a theme for you.
Priority Support
Whether it’s a problem, question or suggestion, you’ll jump to the front of the queue with priority customer support.